In which I feebly hack on a cheap TP-Link MR3020 router.
Project description
I bought this router because I wanted to play around with some hardware. I’d seen a few people flashing it with OpenWRT via easily installed UART headers, and overall it seemed like a pretty tame base to mess with. Plug and play, almost!
I expected to drop into a root shell within about 10 minutes of unboxing it, naturally.
It turned out that I got the new version, which has tiny unsoldered pads (TP1 and TP2 below) for the UART connection rather than holes for pins.
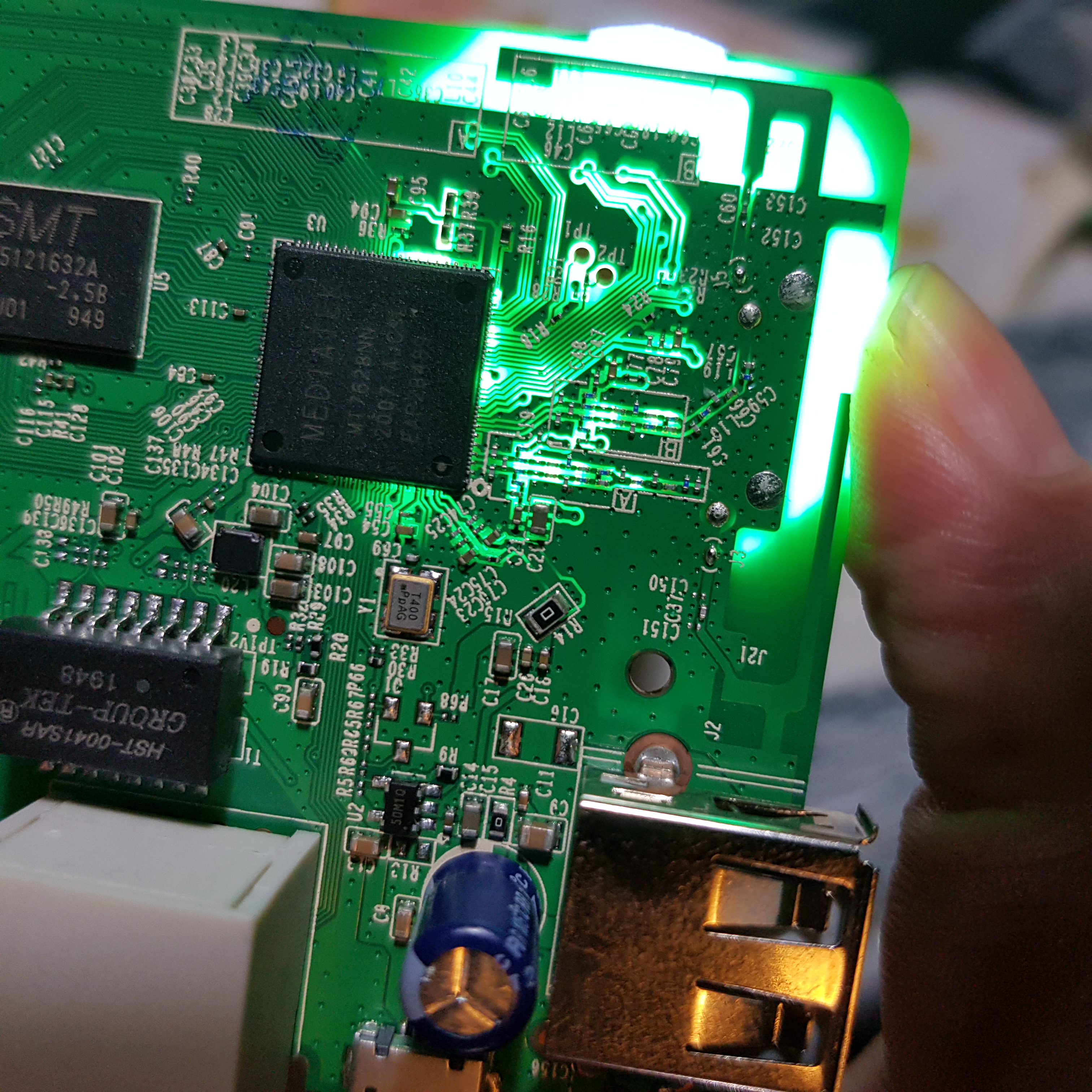
I’m no stranger to soldering but I was concerned that the size of the pads would lead me to bodge the job and somehow break things.
I booted up the router and checked out the web UI. There’s a firmware upload feature, so I decided a more fun plan would be to backdoor the firmware, upload it and see what trouble could be found. Once that was done, I could solder some connectors onto the tiny pads and play with UART. If I broke it at that point, no harm done.
Project goals
- Write usermode backdoor
- Write kernel module with basic backdoor
- Extend kernel module with extra special rootkit functionality (optional)
- Solder stuff on to the tiny pins and drop into a shell that way
- Vulnerability hunt!
- Find a cool final form for it (like turning it into an OpenVPN router) and set it up
Why it’s cool
I’m currently super interested in a) what’s possible with hardware hacking, b) deeply understanding IoT/embedded internals, c) returning to the bosom of C programming, d) learning how to write rootkits/kernel modules, and e) learning how to find vulnerabilities and exploit them!
This little project allows me to pursue all of this at once in a pretty cohesive way, and the hardware is quite a versatile base for making something fun at the end, too.
Documentation and stuff
Some relevant links for this device: